In the world of offensive security, your best tool is usually the one you have on you. While Kali Nethunter is the gold standard, sometimes you just need a lightweight, reliable toolkit that runs on a stock Android device without the overhead of a full chroot environment.
That was the inspiration behind Zinea Mobile Pentest Kit (MPK).
The Vision: Lightweight & Native
I wanted something optimized for modern hardware—specifically the Pixel 7 and above—that didn’t require a custom kernel to be useful. Built with Kotlin and a single-activity architecture, MPK focuses on “living off the land” by leveraging Android’s native binaries and specific APIs to perform network reconnaissance.
What’s Under the Hood?
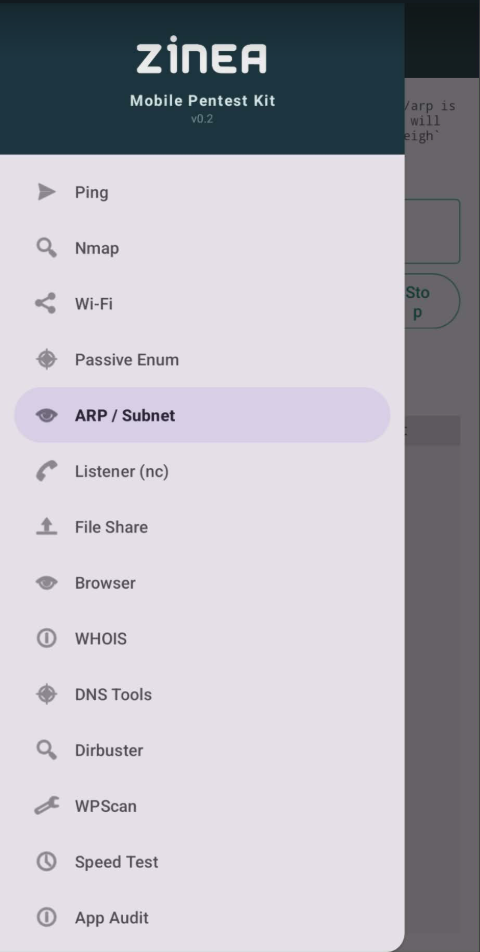
This isn’t just a wrapper for a few shell commands. We’ve packed in a dense feature set for a V1 release:
- Reconnaissance: Integrated Nmap (via a custom Termux-based bundle) and a pure-Kotlin TCP scanner.
- Wireless Testing: A wordlist-based WiFi brute-forcer utilizing the
WifiNetworkSpecifierAPI. - Passive Enum: A listener for MDNS, UPNP, and NetBIOS to map services without sending a single probe.
- Exfiltration & Intercept: A built-in Netcat listener and a high-speed HTTP File Server for moving data off a target network quickly.
- Infrastructure: ARP/Subnet mapping and standard ICMP tools.
- Mobile Audit: A deep-dive permission mapper to audit installed apps for “dangerous” permissions.
Standing on the Shoulders of Giants
A huge shoutout to Claude 4.7 (Anthropic) for its massive contribution to the codebase. It was instrumental in architecting the fragment logic and handling the messy bits of the Android WiFi framework. Yes a lot of tokens were burned!
I’ve also decided to release this under the AGPL-3.0 License. In the spirit of the security community, this ensures that the tool remains open. If anyone wants to use this logic in a network service or a commercial “re-pack,” the code has to stay free and open to the users.
Grab the Binary
You can find the source code and the pre-built APK on GitHub. It’s optimized for arm64-v8a and requires Android 11 (API 30) or higher.
👉 Zinea-Mobile-Pentest-Kit on GitHub
Stay safe, stay legal, and happy hunting. Want to do more with the app? Get a jailbroken phone!