Deploying a high-signal Wazuh + PiHole Defense Alerting System is one of the most effective ways to establish a reliable home Security Operations Center (SOC) without the enterprise noise. When setting up a homelab SIEM, Wazuh is often the first tool recommended. It is a fantastic enterprise-grade, open-source security platform that combines log management, file […]
Building a Mobile Swiss Army Knife: Announcing the Zinea Mobile Pentest Kit (MPK)
In the world of offensive security, your best tool is usually the one you have on you. While Kali Nethunter is the gold standard, sometimes you just need a lightweight, reliable toolkit that runs on a stock Android device without the overhead of a full chroot environment. That was the inspiration behind Zinea Mobile Pentest […]
Poisoning Robinhood: HTML Injection via Metadata
While their systems were not technically breached, on 4/27/2026, Robinhood sent out a swath of phishing emails, being fully signed from their own infrastructure. While phishing emails are not generally interesting, this one is, as the attacker used a novel technique to get these to deliver to the end user, bypassing spam detection, and utilizing […]
CVE-2025-46098 – Achieving RCE via HQueue
On a recent internal penetration test, I ran into something called HQueue (by SideFX), which seems to be some sort of job queueing solution to process workloads. Logo looks something like this: I took a look around the UI and found no authentication which was interesting, and it apparently had a Windows server hooked up […]
How to Root a Pixel 8
There are a ton of guides online for how to root a Pixel 8, but hopefully this is the most straight forward. Honestly this is the way I found to work. However, you can probably skip PixelFlasher and patch the image directly via Magisk. Good luck. Making rooted status/Magisk a bit more obfuscated: If you […]
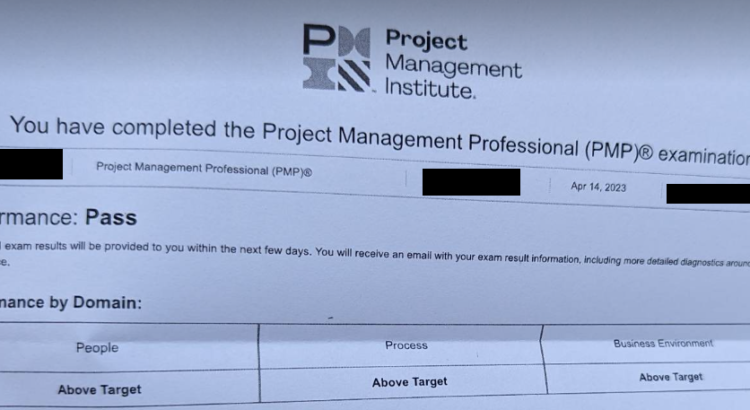
How to Pass the PMP 2023 with x3 Above Target in 3 Weeks
Background I am currently employed full-time, married, and have two children under the age of four. In preparation for the PMP exam, I dedicated approximately 3-4 hours per day on most days and less on weekends. I took four days off prior to the exam and studied for 6-8 hours per day. I have worked […]
Gophish Google Workplaces Sending Profile Tutorial
So you want to send emails with gophish thru Google Workspaces gmail? Nice, because this is the tutorial for Gophish Google Workplaces Sending Profile Tutorial. There’s a few settings you have to enable as followed: Tip, if you’re getting a0 “555 5.5.2 Syntax error”, remove the brackets in the “SMTP from” field Trying to setup […]

2022 CSPM Comparison and Pricing
We recently did a comparison of the top CSPM vendors and did a pricing exercise. If you are unfamiliar, CSPM is more of the compliance side of the house and stands for Cloud Security Posture Management, whereas CWPP stands for Cloud Workload Protection Platform and is more for container and VM scanning. This blog post […]

Phishing O365 with MFA using gophish and Evilginx2
This guide is to help with the setup of gophish to track clicks, and Evilginx2 to capture tokens and creds for O365 logins. This will work even if MFA is enabled on the target accounts. Update as of 10/10/24: There is an official integration now here that you should probably follow, however, the Evilginx setup […]

How to automatically replace cookies in BurpSuite
If you have ever done a phishing exercise for a company, the contract probably said you have to test the creds you get. But what if they’re tokens? Are you going to manually replace them every intercept? No way, that’s extremely slow and error prone. Here’s how to automatically replace cookies in BurpSuite. In the […]
